We infiltrated the criminals' infrastructure.
So you don't have to.
For over 20 years, myNetWatchman has built and maintained a private detection network embedded in the same systems criminals use to test, trade, and monetize stolen credentials and cards.
Most tools alert you at the end.
We intervene at the beginning.
We operate at the Testing stage of the fraud lifecycle — where fraudster intent is visible, losses haven't occurred, and action can still change the outcome.
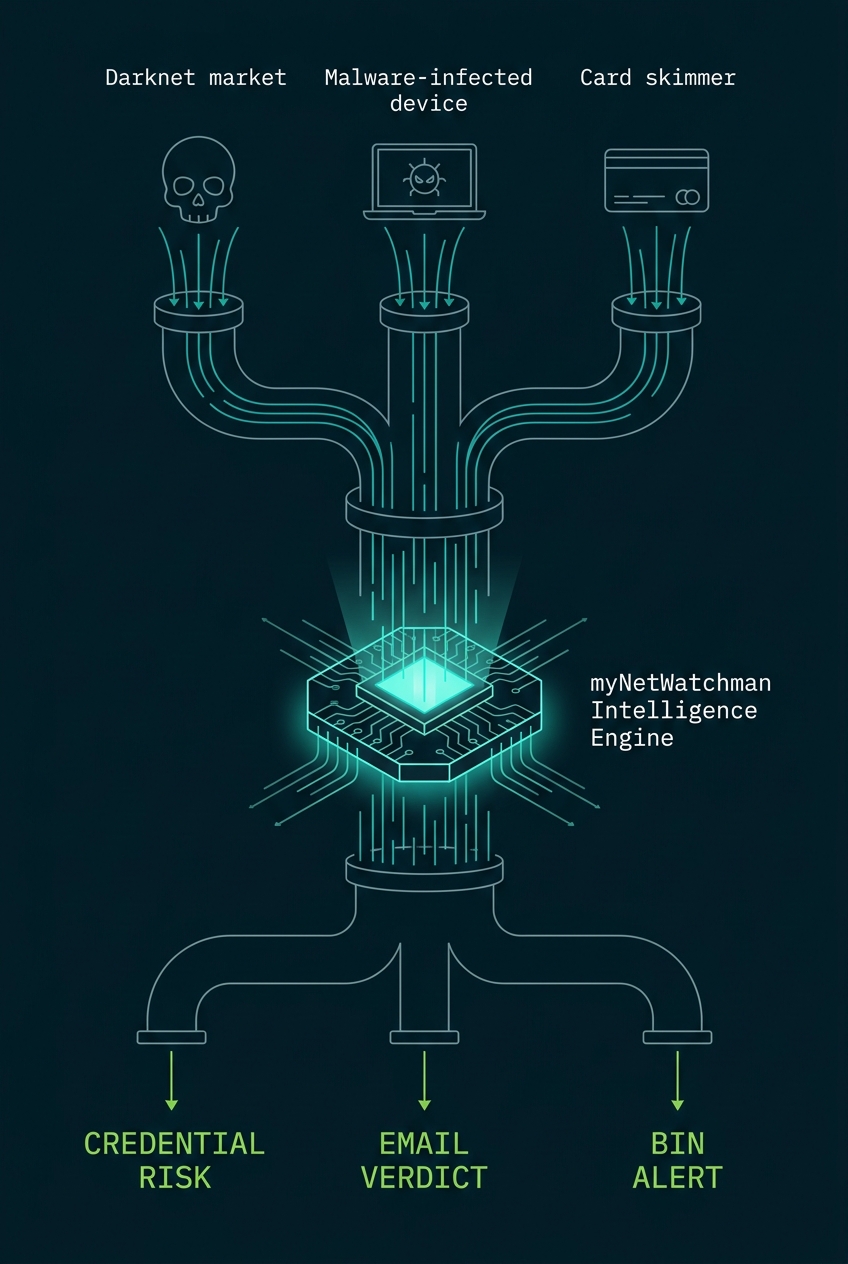
Criminal Infrastructure Monitoring
Our sensors are embedded in criminal networks, phishing schemes, malware-infected devices, and darknet channels. We see credentials and cards as criminals acquire and begin to use them — before victims are aware.
Live Testing Detection
When a criminal begins testing stolen credentials, payment cards, or email addresses, we capture that activity in real time. Data being tested today hasn't appeared in any breach list yet — but we already know about it. This is the intervention window.
Signal Processing & Intelligence Enrichment
Raw detection signals are processed through 20+ years of proprietary intelligence. Velocity analysis, behavioral signals, pattern recognition, and network correlation eliminate false positives and sharpen signal confidence across credentials, cards, and email.
Delivery via API or Webhook — In Seconds
Actionable intelligence delivered to your fraud stack via API or webhook. Integration typically completes in days. Alerts arrive within seconds of detection — not days or weeks.
You Act. Fraud Stops.
Acting on confirmed criminal behavior — not probability scores — your team applies targeted controls only where needed. Fewer false positives. Better customer experience. Real fraud prevention.
The intelligence advantage in concrete terms.
Simple to deploy. Powerful from day one.
Works alongside your existing fraud stack — no replacement required.
REST API & Webhooks
Simple, well-documented API for real-time lookups. Push-based webhooks for instant alerting. Works with any platform.
Days to Integrate
Typical integration completes in days, not months. No rip-and-replace — enhances what you already have.
Works With Your Stack
Complements existing fraud tools, identity platforms, and authentication providers without disrupting workflows.
Minimal Data Sharing
Credential audits and active directory monitoring require no PII. Email reputation checks use only the email address itself. Privacy-safe by design.
See how it works on your data.
A free POC gives you real results against your own credential set — no commitment required.
